ElcomSoft iOS Forensic Toolkit performs full file system and logical acquisition of iPhone, iPad, and iPod Touch devices. Image device file system, extract device secrets (passwords, encryption keys, and protected data), and decrypt the file system image.
- Download Link
- Features
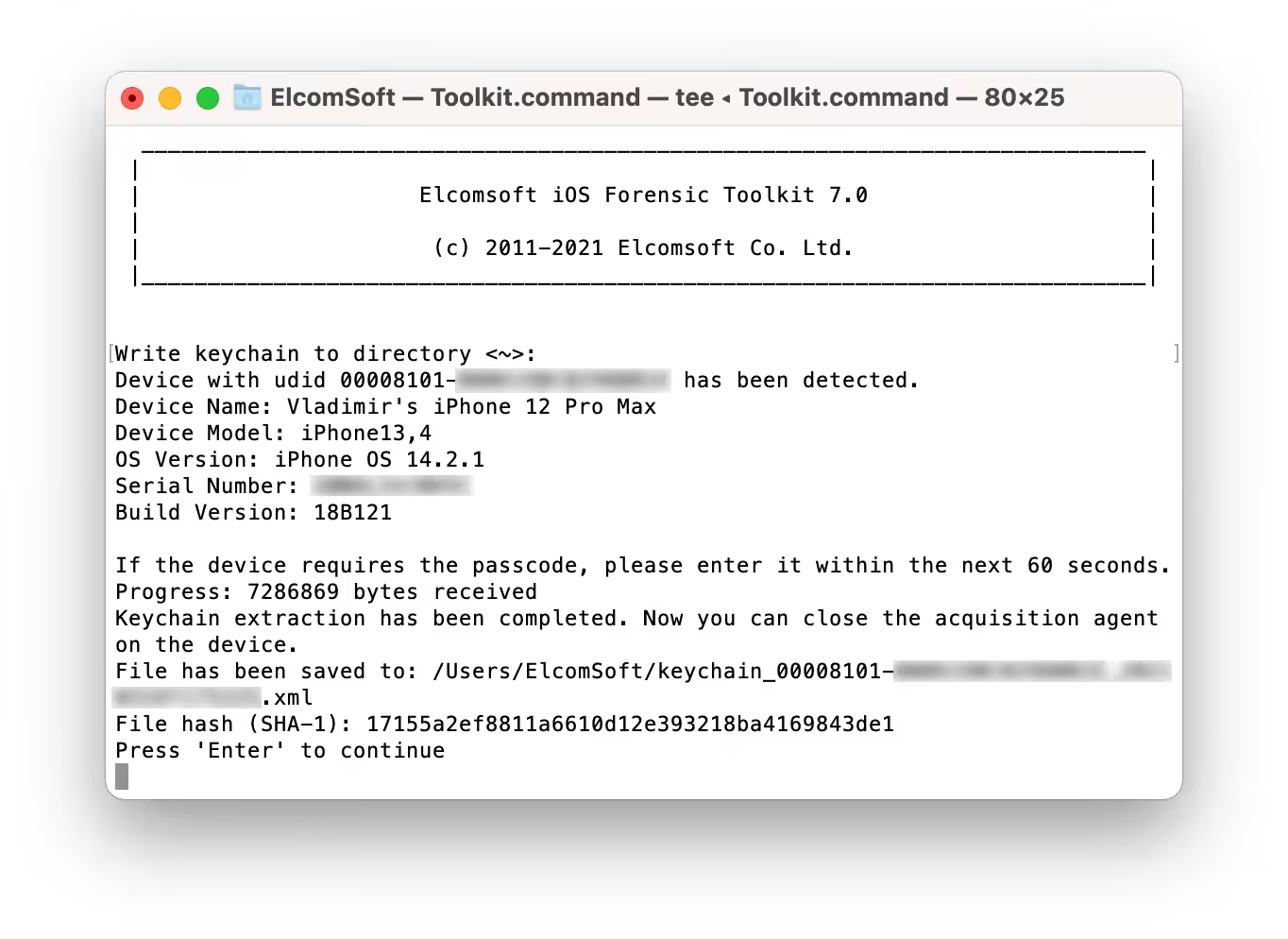
- Screenshots
- Whats new?
- Forensic Access to iPhone/iPad/iPod Devices running Apple iOS: Perform the complete forensic acquisition of user data stored in iPhone/iPad/iPod devices. Elcomsoft iOS Forensic Toolkit allows imaging devices’ file systems, extracting device secrets (passcodes, passwords, and encryption keys), and accessing locked devices via lockdown records.
- Full File System Extraction and Keychain Decryption Without a Jailbreak: iOS Forensic Toolkit fully supports the extraction of all jailbroken devices for which a jailbreak is available. Full file system extraction and keychain decryption are available for jailbroken devices. All public jailbreaks are supported.
- Unlock and Imaging of Legacy Devices: iPhone 4, 5, and 5c: Passcode unlock and imaging support are available for legacy iPhone models. The Toolkit can be used to unlock encrypted iPhone 4, 5 and 5c devices protected with an unknown screen lock passcode by attempting to recover the original 4-digit or 6-digit PIN. This DFU attack works at the speed of 13.6 passcodes per second on iPhone 5 and 5c devices and takes only 12 minutes to unlock an iPhone protected with 4-digit PINs. 6-digit PINs will take up to 21 hours.
- Extended Logical Acquisition: iOS Forensic Toolkit supports logical acquisition, a simpler and safer acquisition method compared to physical. Logical acquisition produces a standard iTunes-style backup of information stored in the device, pulls media and shared files, and extracts system crash logs. While logical acquisition returns less information than physical, experts are recommended to create a logical backup of the device before attempting more invasive acquisition techniques.
- Added support for Apple devices running iOS 14.0 through 14.3 via extraction agent (full file system and keychain)
- Added support for A14 Bionic devices (full iPhone 12 range and iPad Air 4th generation)
- Gapless jailbreak-free extraction coverage for all devices running iOS 9.0 through 14.3
- Minor bug fixes and improvements